AI MONITORING · GUARDRAILS ALERTS
Catch policy events before they become headlines.
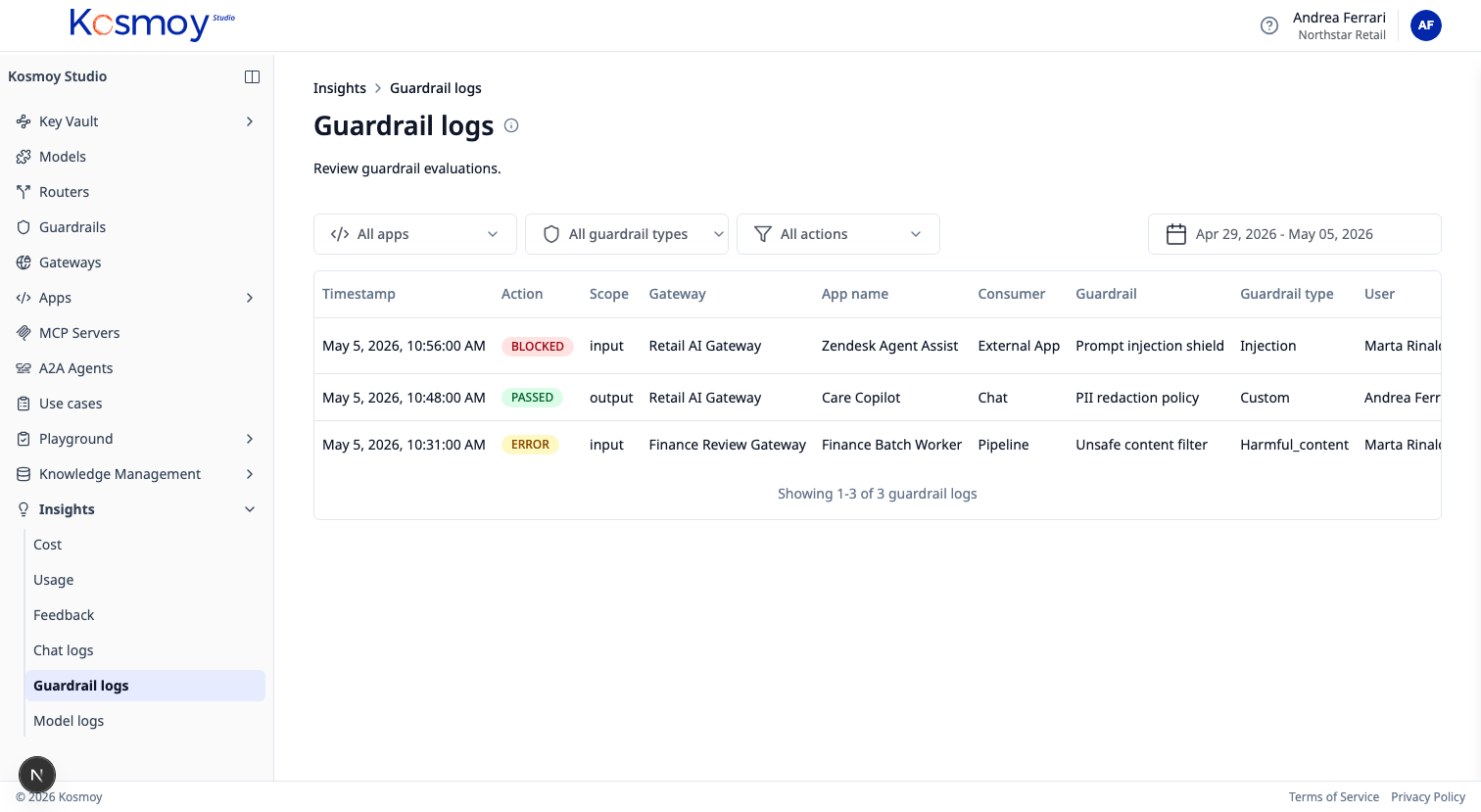
Every guardrail decision from the Gateway, surfaced in real time and joined to the prompt, the user, the app and the use case.
Guardrails enforce policy in the call path. Guardrails Alerts roll the resulting events up — toxic language hits, PII detections, prompt injection attempts, policy compliance triggers, custom rule events.
Searchable, exportable, deliverable to your existing SIEM and chat ops, and bound to the AI Act dossier as evidence.
What it does.
Five categories
Toxic language, PII, prompt injection, policy compliance, custom rules.
Real-time delivery
In-dashboard, email, webhook to Slack / Teams, SIEM forwarding.
Drilldown to call
Click an alert to see the prompt, response and routing decision.
Per-app and per-user views
Spot which app or user is most often triggering each rule.
Trend lines
Alert rate over time, by category and app. Catch regressions early.
Dossier evidence
Every alert is structured evidence for AI Act Article 12.
Module questions, answered straight.
What kinds of alerts can I get?
Toxic language hits, PII detection, prompt injection attempts, policy compliance triggers, custom rule events. Each alert links back to the prompt, the user, the app and the use case.
How are alerts delivered?
In-dashboard, email, webhook to Slack / Teams, and structured events into your SIEM (Splunk, Datadog, Elastic).
Do alerts feed the AI Act dossier?
Yes. Every guardrail decision is captured as evidence — actor, system, outcome, timestamp — and connects to the use case for Article 12 record keeping.
See real-time guardrail events.
Walk through alert delivery, drilldown and SIEM forwarding.