AI GOVERNANCE · A2A AGENTS GATEWAY
Govern agent-to-agent traffic.
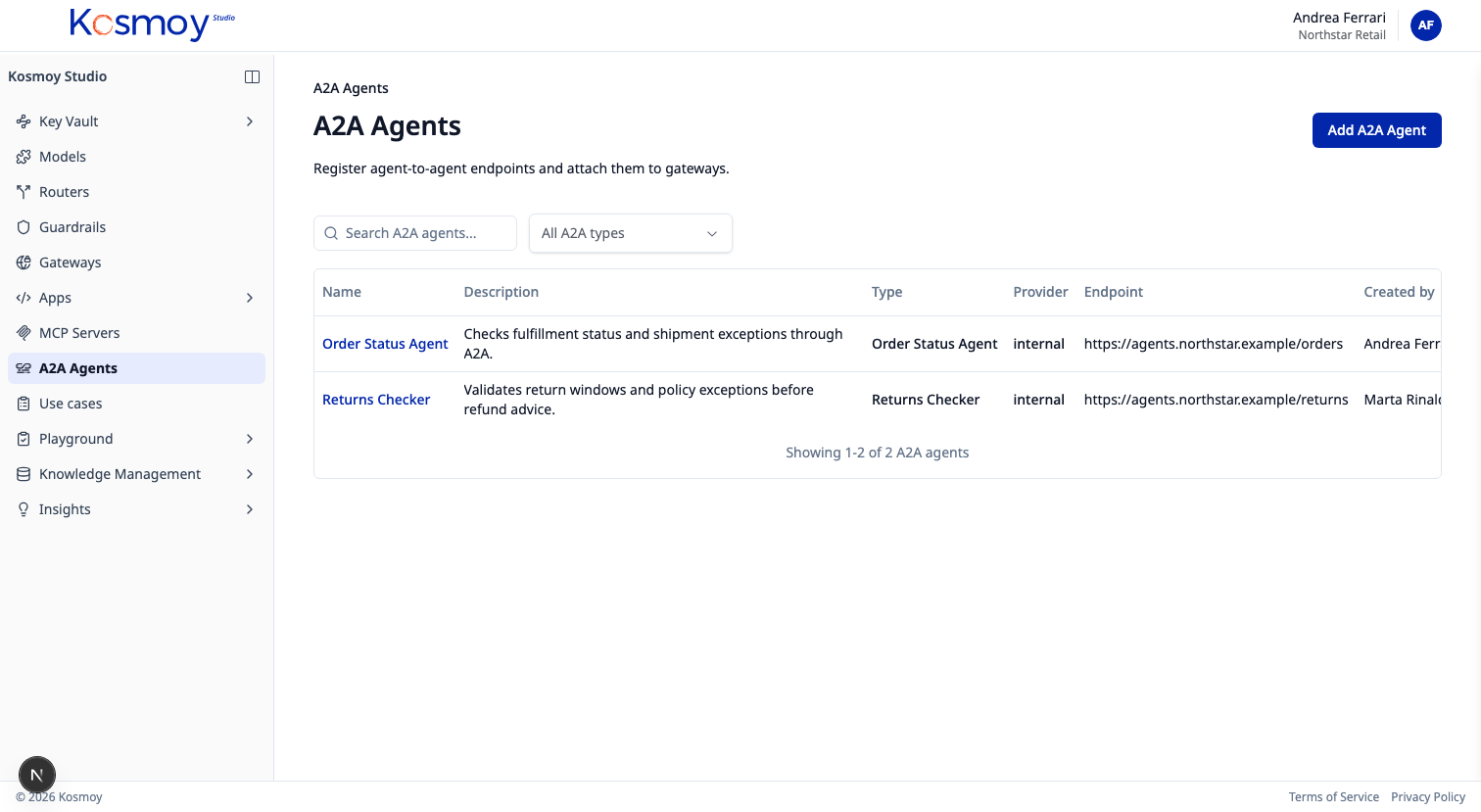
Internal agents and external A2A peers, behind one policy point. Same audit trail as LLM and MCP traffic.
When agents start calling other agents, governance has to follow the conversation. The A2A Agents Gateway sits between your agents and any A2A peer — internal or external — applying auth, allow-list and audit on every handshake.
When the calling agent runs inside an Action Capsule, the Gateway is its only egress. When the agent runs outside, the Gateway still mediates traffic with peers.
What it does.
Per-agent allow-list
Each agent has a list of A2A peers it's approved to reach. Nothing else.
Run-scoped authorisation
When the caller is in a Capsule, every A2A handshake is admitted run-by-run.
Mutual authentication
Identity exchange between Kosmoy and external peers. No anonymous A2A.
Full audit
Every handshake captured with caller, peer, run identifier, outcome.
External peer discovery
Approved peers register in the Agent Registry. Discovery is governed.
Policy hooks
Inject policy checks before any state-changing A2A call lands.
Module questions, answered straight.
What does the A2A Agents Gateway govern?
Agent-to-agent traffic — your internal agents talking to other internal agents, and your agents talking to external A2A peers. Same policy point, same logging, same audit trail as LLM and MCP traffic.
Can it gate which agents can call which?
Yes. Per-agent and per-peer allow-lists, plus run-scoped authorisation when the call originates from inside an Action Capsule.
Does it cover the A2A protocol specifically?
Yes. The Gateway speaks A2A on top of the same auth, RBAC and audit primitives the rest of Kosmoy uses.
See A2A traffic governed.
Walk through internal-internal, internal-external and run-scoped authorisation.